Pass Inspections, Reduce Risk: NYC Access Control Compliance Steps for 2026
Whitestone, United States – February 23, 2026 / Streamline Telecom /
Streamline Telecom has released a 2026 compliance education guide built for New York businesses that need access control decisions to stand up to audits, inspections, and risk reviews. The guide explains what compliance-ready access looks like in real buildings—what to document, what to test, and what to avoid—so property teams can reduce exposure without overbuilding.
The release supports organizations across the New York City Metropolitan Area that must answer to tenants, boards, insurers, and internal security teams. It is written for practical operators: building owners, facilities leaders, construction managers, and contractors who need a system that works, records cleanly, and stays defensible over time.
The guide is anchored by Streamline Telecom’s field experience as an access control installation service provider known for timelines, responsive communication, and clean installation standards.
Industry Challenge
In 2026, New York businesses face a sharper compliance lens. Security incidents trigger faster scrutiny. Tenant demands are higher. Insurance and risk teams increasingly ask for proof—not promises. The difference between “installed” and “compliant” often comes down to documentation, configuration discipline, and repeatable maintenance.
Across the New York City Metropolitan Area, many access control failures are not hardware failures. They are process failures: credential lists that are never cleaned, doors that do not fail safe as expected, audit trails that cannot be produced, and systems that drift out of alignment after renovations. Institutions and risk-averse buyers need a framework that makes compliance predictable, not reactive.
This guide lays out that framework with clear standards, practical checklists, and implementation guidance for Access Control Systems in commercial environments.
Compliance Starts With System Definition, Not Hardware
Access control systems are sometimes referred to as card access systems, but compliance depends on more than a reader and a badge. A compliant Access Control System is one that reliably controls entry, records events, supports emergency egress, and proves what happened when questioned later.
Compliance expectations vary by building type, tenant profile, and internal policies. A medical suite will carry different requirements than a warehouse. A financial services floor will demand tighter credential governance than a typical office. Even within the same portfolio, different entrances may require different lock hardware due to door construction and life-safety constraints.
The guide’s first principle is simple: define the control objective for each opening. That objective must include who can enter, when they can enter, how entry is logged, what happens during power loss, and how exceptions are approved. Without that definition, procurement turns into guesswork, and compliance becomes a scramble during inspections.
The Compliance Core: Audit Trails, Egress, and Credential Control
Most risk reviews focus on three questions. First, can unauthorized entry be prevented with consistency? Second, can safe exit be ensured during emergencies? Third, can access history be produced quickly and credibly?
Those questions map directly to practical system requirements. Audit trails must be enabled and retained. Door states must behave correctly under fire alarm or power loss conditions. Credential governance must reflect real staffing and tenancy changes.
A compliant program depends on repeatable operating habits more than special equipment. Systems that look modern can still fail a compliance review if the database is a mess, access levels are overly broad, or logs are not retrievable.
In the New York City Metropolitan Area, this matters even more because buildings undergo constant change—tenant fit-outs, door replacements, and network changes that can quietly break integrations. A compliance-ready system anticipates change and is designed to be verified.
Access Control Components and Where Compliance Breaks
Compliance risk often shows up at the seams between components. Each core element has a predictable failure mode when neglected or misconfigured.
Access control keypads are sometimes installed to speed entry or reduce credential issuance, but they can also increase risk when codes are shared or never rotated. Some models use obscured or changing number orders to reduce observation-based compromise. Even with better hardware, compliance still relies on code management discipline: rotation schedules, user-level accountability, and removal of codes for separated staff.
Electric lock hardware is where compliance meets life safety. Electromagnetic locks, electric strikes, and electric exit devices behave differently under power loss and emergency conditions. The lock mechanism must match the door construction and the building’s egress requirements. Poor alignment, improper mounting, or incorrect power supplies lead to failures that show up during inspections or, worse, during an incident.
Proximity cards and smart cards introduce a different kind of risk: credential sprawl. RFID cards, NFC smart cards, and key fobs are convenient, but they require clean deactivation workflows. Organizations that cannot reliably deactivate credentials for terminated employees are not compliant in any meaningful sense, even if the hardware is premium.
Biometric readers reduce credential sharing but raise their own governance issues. Enrollment must be controlled, privacy policies must be clear, and fallback methods must be documented. In risk-averse environments, biometrics are typically paired with cards to support multi-factor entry. Compliance depends on documented enrollment, consistent reader performance, and clear exception handling.
The access control server is the system’s “brain,” recording activity and distributing data to control panels. Compliance can fail if logs are not retained, backups are not tested, or updates are ignored. Whether a system is cloud-managed or on-premise, the server layer must be treated as critical infrastructure, not a set-it-and-forget-it device.

The 2026 Documentation Standard: What to Keep and Why
When compliance questions arrive, the right response is paperwork that matches reality. The guide sets a baseline documentation package that property teams can maintain without bureaucracy.
A defensible file should include door schedules, hardware lists, wiring paths, panel locations, and configuration exports. It should also include credential policies, access level definitions, and an incident response workflow. For institutions, that documentation becomes the “single source of truth” during audits, security reviews, or insurance inquiries.
Documentation also reduces vendor lock-in. When system details are organized and complete, future upgrades are faster and less expensive. In the New York City Metropolitan Area, where renovations are frequent, good documentation prevents a simple door replacement from turning into a system-wide outage.
Short records are better than no records. The point is clarity: what is installed, how it is configured, and how it is maintained.
Practical Compliance Checklist for Property Managers
Compliance improves when routine checks are scheduled and owned. The guide includes a lightweight checklist designed for building teams and vendors to share.
-
Confirm access logs are enabled and retrievable for key doors
-
Review and deactivate stale credentials on a set schedule
-
Test door release behavior during power-loss and fire alarm conditions
-
Verify reader and keypad function, including lock engagement alignment
-
Confirm server backups, updates, and admin access controls
This checklist is intentionally short. It is meant to be repeatable across sites, especially for multi-property operators in the New York City Metropolitan Area.
After each cycle, notes should be stored centrally. That trail becomes evidence of ongoing compliance, not a one-time installation claim.
Cloud vs On-Premise: Compliance Tradeoffs That Matter
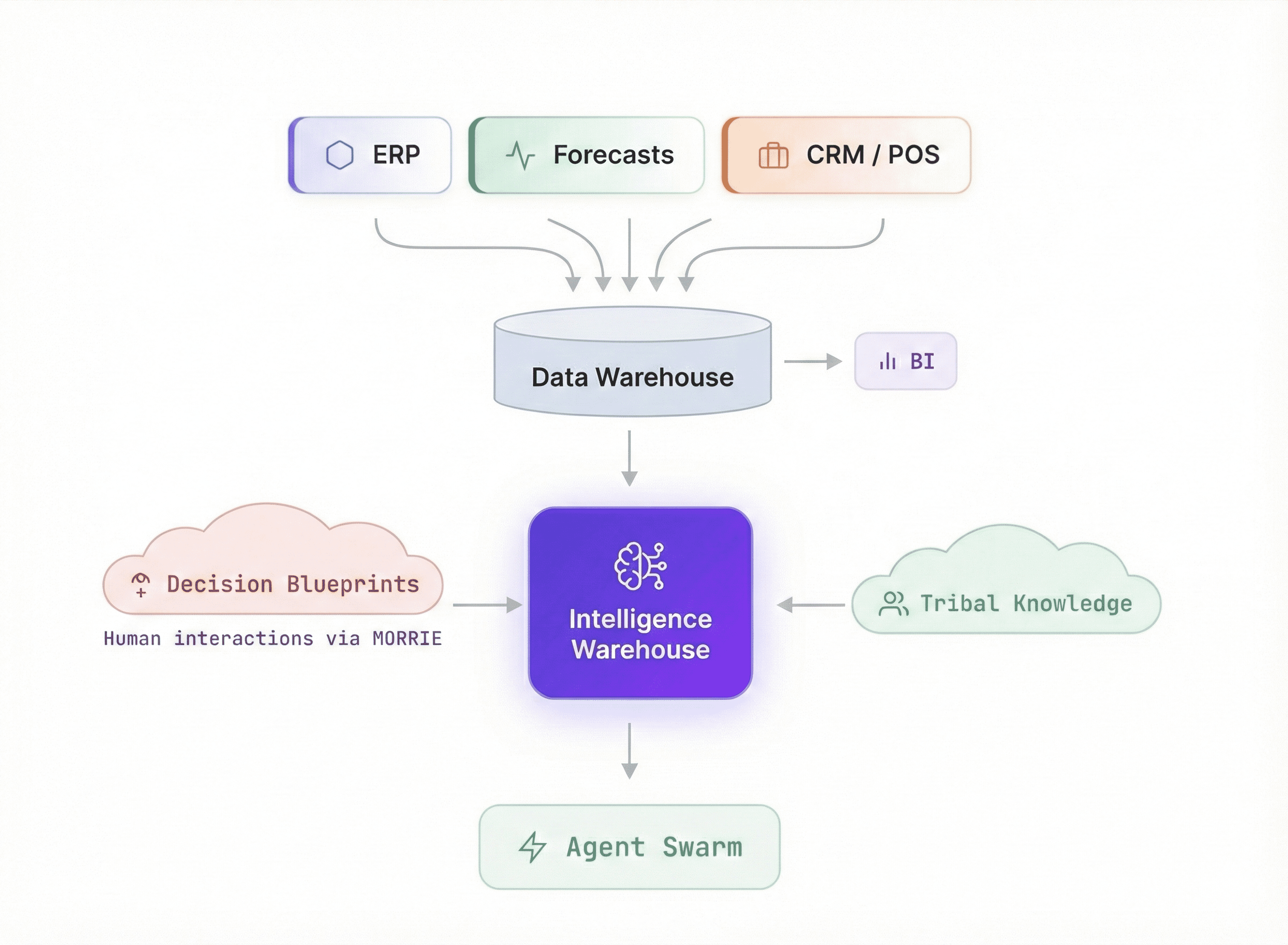
Streamline Telecom works with Avigilon Alta (formerly Openpath) for cloud access control and Avigilon Unity for on-premise video security and access control. Both can support a compliant program when designed correctly, but their compliance responsibilities differ.
Cloud platforms like Alta can simplify patching and remote management. When updates are delivered consistently and systems remain current, risk decreases. Remote dashboards also make it easier to verify events and manage credentials across multiple sites.
On-premise platforms like Unity can be the right fit for organizations that require local control, specific network rules, or tighter internal governance. The tradeoff is increased operational responsibility: patch scheduling, server health monitoring, and backup discipline are essential.
The key point is not cloud versus on-premise. It is accountability. Compliance depends on clearly assigned ownership of updates, logs, admin access, and emergency behavior testing.
Building for Inspections: Egress, Power, and Fail-Safe Behavior
Many compliance failures show up during inspection because the system’s emergency behavior was never tested in the real building. Access Control Systems must respect egress and life-safety requirements. That includes proper release during fire alarm events, appropriate signage where required, and correct fail-safe or fail-secure behavior based on door type and code requirements.
Magnetic locks are common in commercial settings, but they require correct installation and integration to meet safety expectations. Power supplies must be sized correctly. Battery backup must be maintained. Wiring must be clean and traceable. These details separate a system that “works most days” from a system that can be defended when questioned.
In the New York City Metropolitan Area, inspectors and building management teams expect clean workmanship and predictable behavior. This is not cosmetic. Clean installation reduces troubleshooting time and supports reliable operation under stress.
Vendor Selection for Risk-Averse Buyers: What to Ask Before Award
Risk-averse buyers and institutions should evaluate access control vendors the same way they evaluate other critical infrastructure partners. The guide encourages decision-makers to ask process questions, not marketing questions.
A reliable access control company should be able to explain documentation standards, testing protocols, and maintenance ownership without hesitation. The proposal should spell out how logs are retained, how credentials are managed, and how emergency behavior is verified.
When a vendor cannot describe how compliance will be maintained after installation, the system becomes a liability. This is especially true for institutions and multi-tenant buildings in the New York City Metropolitan Area, where turnover and change are constant.
Streamline Telecom’s core difference—The Most Reliable & Fair—shows up here. Timelines are honored. Communication stays fast. Systems are organized, labeled, and built to be maintained. Compliance becomes simpler when execution is disciplined.
Ongoing Compliance: Maintenance as a Control, Not an Expense
Compliance is not a certificate earned at install. It is a condition maintained over time. A quarterly review cadence for access levels, admin accounts, and door behavior keeps systems aligned with real occupancy.
Firmware updates and security patches should be scheduled, not postponed. Backup verification should be tested, not assumed. Credential issuance should follow a workflow with approvals, not ad-hoc requests.
When these habits are in place, the system becomes predictable. Incidents are easier to investigate. Audits are easier to pass. Total cost of ownership drops because emergency service calls become rare.
For additional guidance on choosing and maintaining Access Control Systems, Streamline Telecom’s resource hub includes details on access control system installation, planning and modernization options.

About
Streamline Telecom has been at the forefront of commercial telecom installation, business security, access control, and video systems, consistently striving to deliver solutions and services that improve the way clients achieve remodeling success. With a relentless focus on integrated planning, the company has refined a process that eliminates costly surprises and creates better outcomes.
Across the New York City Metropolitan Area, Streamline Telecom is known for disciplined timelines, fast responsive communication, and exceptionally clean, organized installations that make facilities teams look prepared and professional.
Conclusion
The 2026 NYC Access Control Compliance Guide is designed to reduce uncertainty for institutions and risk-averse buyers. It clarifies how Access Control Systems should be defined, installed, documented, and maintained so compliance can be demonstrated quickly—without scrambling when an audit or incident hits.
For New York businesses planning new installs, upgrades, or standardization across multiple sites, Streamline Telecom provides clear scoping, disciplined execution, and maintenance-ready delivery that supports long-term compliance.
Decision-makers can review next steps and connect through Streamline Telecom’s Google Business Profile

Contact Information:
Streamline Telecom
152-53 10th Ave
Whitestone, NY 11357
United States
Sean Nolan
https://www.streamlinetelecom.com/